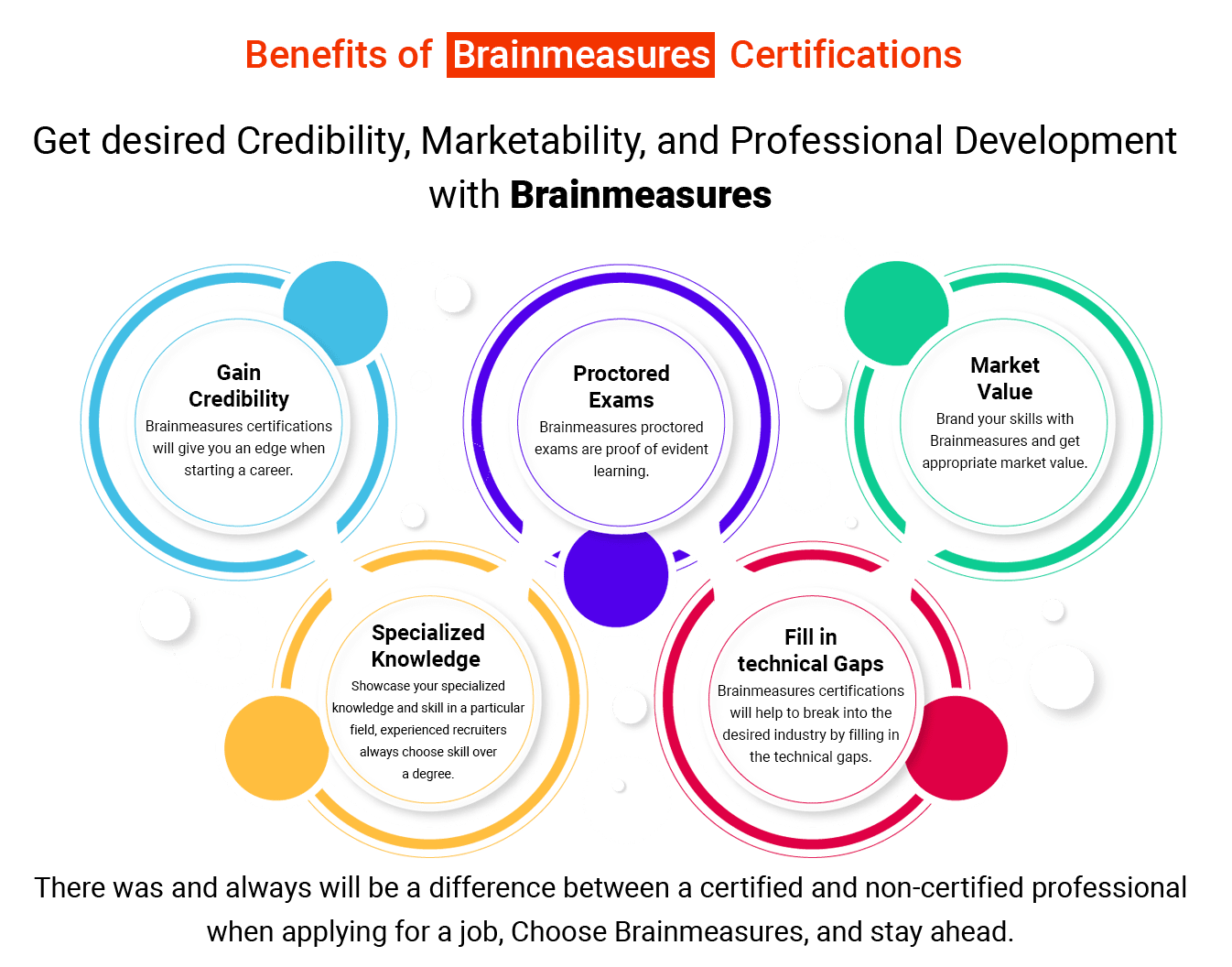
THIS CERTIFICATION IS AUTHENTIC AND ACCEPTED BY EMPLOYERS. HOW ? Read more
What You get
with this Course
Penetration Testing with Python 3 I Cyber Security Certification Course
WHY IS THIS VIDEO TRAINING ONLINE CERTIFICATION HIGH IN DEMAND?
What is Cybersecurity?
Computer security (also known as cybersecurity) or information technology security refers to safeguarding computer systems and networks against information disclosure, theft, and damage to their hardware, software, or electronic data, as well as from disruption or misdirection of the services they offer (IT security).
For systems connected to the internet, including their hardware, software, and data, cybersecurity is the defense against cyber threats. This method is used by both individuals and companies to stop unauthorized access to data centers and other digital systems.
A strong cybersecurity strategy can provide a good defense against harmful attacks that aim to access, change, remove, destroy, or extort sensitive data and systems that belong to a company or user. Security precautions are crucial in thwarting attempts to disable or damage a system's or device's functionality.
Cybersecurity is the line of defense against damaging attacks on internet-connected devices and services by hackers, spammers, and cybercriminals. The procedure is used by businesses to protect themselves from phishing scams, ransomware attacks, identity theft, data breaches, and financial losses.
You only have to look around to realize how reliant on technology the world is today.
What is Python 3?
Python is a general-purpose, high-level programming language. Its design philosophy prioritizes code readability and heavily employs indentation.
Python has dynamic typing and garbage collection. Functional, object-oriented, and structured (particularly procedural) programming paradigms are among the ones it supports. Python has advanced in recent years to rank among the programming languages that are most often used globally. It is utilized in everything, including machine learning, software testing, and website building. It can be used by developers and non-developers alike.
Python is a high-level, all-purpose programming language. Its design philosophy places a strong emphasis on indentation and prioritizes code readability. Python has a big collection and dynamic typing. It supports a variety of programming paradigms, including functional, object-oriented, and structured (especially procedural) paradigms.
In recent years, Python has progressed to become one of the most widely used programming languages worldwide. Everything uses it, including website development, software testing, and machine learning. Both developers and non-developers can use it.
What is the role of Python in Cybersecurity?
A little programming language is Python. There isn't a lot of complex code required. It speaks in simple terms. As you can see, Python is simple, which makes it easier to learn than other programming languages like C, Java, etc. Few lines of code are required for Python.
Automatic Memory Management
Python includes an integrated memory management system. As a result, developers won't have to worry as much about memory management, which is quite advantageous. There are no issues with segmentation or caching.
Carrying out a range of cyber security tasks
Given that it can perform a variety of cybersecurity tasks like malware analysis, scanning, and penetration testing, Python is a very useful programming language for cybersecurity professionals. Python is frequently recommended as the first language people who are new to cybersecurity should learn due to its widespread use and simple learning curve.
What is penetration testing in python?
Penetration testing, often known as a pen test or ethical hacking, is the authorized simulation of a cyberattack on a computer system that is used to assess the system's security. An assessment of vulnerabilities is not the same as this. The test is conducted in order to identify both strengths and weaknesses, enabling a thorough risk analysis. Vulnerabilities, which are another name for weaknesses, include the potential for unauthorized parties to access the system's functions and data.
Python is the top language for information security and penetration testing. Numerous Python-based programs offer proxy services, may produce random data to detect flaws and problems, and even whole exploit frameworks.
Python is a great language to learn if you're an experienced penetration tester interested in customizing or creating your own tooling. It has clear code, a modular design, and many libraries you can use as a starting point to create your own security tools. These libraries range from modules that carry out straightforward I/O operations to libraries that generate API calls for particular systems.
What is the importance of penetration testing in python?
Sustains ongoing faith
Customers may start to lose faith in a firm as a result of a data breach, which can damage its brand and generate further losses. Run regular pen tests in order to ensure security and keep clients' faith in your business. A thorough security audit reassures clients, suppliers, partners, and stakeholders.
In order to Recognize and Address Vulnerabilities
A network or system that supports the entire business is frequently designed and implemented with defects and weaknesses. These flaws can be exploited by hackers that stay up to date with technology and rely on their expertise in finding and exploiting known vulnerabilities in these systems.
Make dependable security provisions
A penetration test gives your company valuable information about discovered security flaws and their current and potential effects on the system's performance. An experienced penetration tester will provide you with a list of recommendations outlining the seriousness of the issue, the deadline by which it should be fixed, and how to create a strong information security system that will enable you to prioritize your future cybersecurity efforts.
The focus is still on manual skills despite the use of automated technologies, making the professional expertise and experience of the testers the most valuable asset. For this reason, pick a reputable and experienced company to perform your penetration tests.
Why Brainmeasures?
Brainmeasures is an ISO-certified company that offers you high-end certification courses and many other services to boost your career. We hire experienced and qualified experts to create in-depth and prominent content courses to train our learners whether they are amateurs or have some experience in the field. We provide the best courses to offer you top-notch skills with a broad scope.
To check these services, click on the following links:
1300 eBook Courses (Technical and Non-Technical)
20000+ Video Courses (Technical and Non-Technical)
Course Syllabus
| Getting Started | 11 lectures | 17 mins |
| HTML and foundation | 11 lectures | 17 mins |
| Some title goes here | Preview | 01:42 |
| Welcome guide document | 10 Pages | |
| Some title goes here | 07:42 | |
| 2 Some title goes here | 07:42 | |
| Hello Some title goes here | 07:42 | |
| This is Some title goes here | 07:42 |
| CSS and foundation | 17 lectures | 87 mins |
| Some title goes here | Preview | 01:42 |
| Welcome guide document | 10 Pages | |
| Some title goes here | 07:42 | |
| 2 Some title goes here | 07:42 | |
| Hello Some title goes here | 07:42 | |
| This is Some title goes here | 07:42 |
| Making Responsive Website | 17 lectures | 87 mins |
| Some title goes here | Preview | 01:42 |
| Welcome guide document | 10 Pages | |
| Some title goes here | 07:42 | |
| 2 Some title goes here | 07:42 | |
| Hello Some title goes here | 07:42 | |
| This is Some title goes here | 07:42 |
| Learn Sass less Scss | 17 lectures | 87 mins |
| Some title goes here | Preview | 01:42 |
| Welcome guide document | 10 Pages | |
| Some title goes here | 07:42 | |
| 2 Some title goes here | 07:42 | |
| Hello Some title goes here | 07:42 | |
| This is Some title goes here | 07:42 |
| Learn about Cpanel and file uploads | 17 lectures | 87 mins |
| Some title goes here | Preview | 01:42 |
| Welcome guide document | 10 Pages | |
| Some title goes here | 07:42 | |
| 2 Some title goes here | 07:42 | |
| Hello Some title goes here | 07:42 | |
| This is Some title goes here | 07:42 |
Do you want this course
to learn
LIVE
?
Enroll in this course now and avail all the benefits.
Learn from industry
Experts
LIVE
?
Learn One-to-One Live Course - Coming Soon.



Brainmeasures Certifications are acknowledged globally because the tests are conducted under the strict vigilance of trained proctors and are recorded which makes Brainmeausres testing system the most authentic testing platform.
Enroll NowOur Hiring Partners
Brainmeasures certified Professionals work with global leaders.
Corporate Training
If you want to give the Trending technology experience to your esteemed employees, we are here to help you!
CONTACT CORPORATE CO-ORDINATOR
What makes Penetration Testing with Python 3 I Cyber Security Certification Courseunique?
VIDEO ONLINE COURSE
The video online course is well-structured and comprehensive.
EASY TO UNDERSTAND
The topics are organized in proper sequence to enable the candidate understand them easily.
SELF-EXPLANATORY
Easy to understand and implement in real life.
MORE ATTRACTIVE
Sufficient pictures, tables, graphs have been provided to make this online Course more attractive to the readers.
PROCTOR SURVELIANCE
Final certification exam conducted under surveillance of trained human proctor.
HARD COPY SHIPPED
We will ship your hard copy anywhere you ask for.
-

- We will ship your hard copy anywhere you ask for.
- SAMPLE HARDCOPY CETIFICATE
-

- Immediately after taking the test you can check your scores with detailed.
- Immediately download soft copy certificate.
- VIEW ANALYSIS REPORT
-

- ENROLL FOR Penetration Testing with Python 3 I Cyber Security Certification Course - VIDEO COURSE AND CERTIFICATION PROGRAM
- REGISTER NOW
-

- Online Video course by Highly qualified Trainers.
-

- If you have any query our trainers are accessible easily.
- Send your questions and get answers within 7 working days.
-

- Final exam is proctored – you will be monitored throughout, this is done using our high-end Proctor software, so that you need not go to any special location but take it from your own PC.
- This testing format matches world-class testing standards.
- Certificate will mention wording proctored to prove the authenticity of your knowledge.
-

- You can take any number of retakes if you are not satisfied with your score or failed to pass.
- Test re-takes are paid, each retake is worth $ 50.
-

- Earn high.
- Brainmeasures certificates are honoured by employees worldwide.
- Get desired position in your organization.
TAKE A FREE TEST
Penetration Testing with Python 3 I Cyber Security Certification Course
Take free practice test now
Reviews ( click here to Read all )
Why choose Us
In today’s corporate world, a single wrong decision can cost you millions; so you cannot afford to ignore any indemnities you may incur from a single wrong hiring decision. Hiring mistakes include the cost of termination, replacement, time and productivity loss while new employees settle into their new job.
Our Mission
Our Mission is simply to help you attain Course Name knowledge which is at par with best, we want to help you understand Course Name tools so that you can use them when you have to carry a Course Name project and make Course Name simple and learnable.